Litecoin’s active addresses count hits 8-month high; surges past 141K

Litecoin’s on-chain metrics have slowed down after its second block reward halving in 2019. However, on a positive note, the network’s active addresses have now surged to an 8-month high of 141,676.
According to data gathered from BitInfoCharts, the number of unique [from or to] addresses per day rose from a low of 34,273 on 1 January.
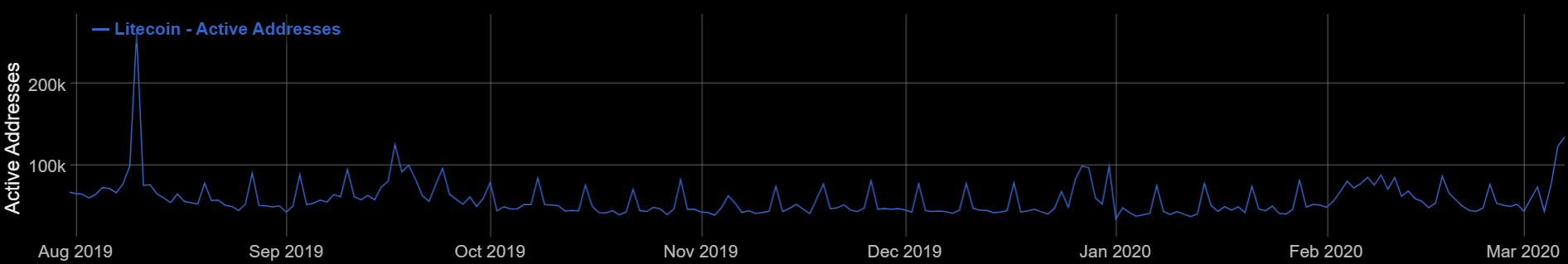
Source: BitInfoCharts | Litecoin | Active Addresses Chart
The active address figures last spiked on 10 August, five days after the scheduled halving, a day when it rose to 262,573. Following the same, the address count declined, apart from one instance on 17 August 2019 when the number of unique addresses shot up to 125,420.
Since then, for the most part, the numbers have been on a decline, similar to other metrics on the Litecoin network. Interestingly, the average transaction value graph had also recorded a mild spike following the aforementioned increase, at press time.
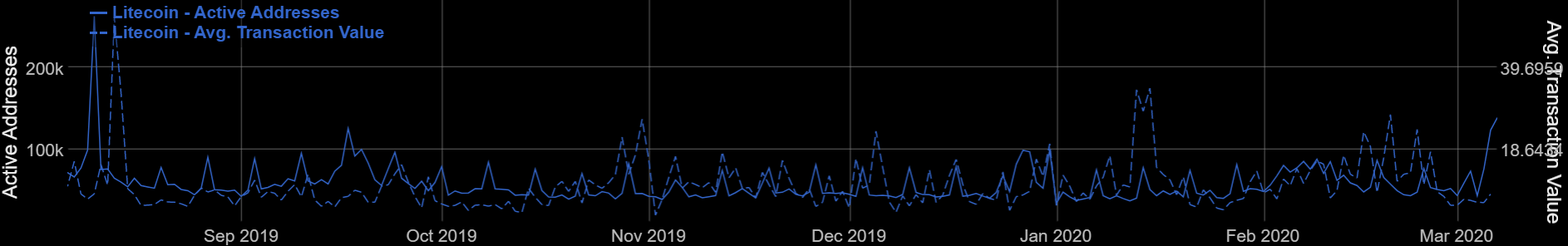
Source: BitInfoCharts, Litecoin | Active Address | Avg. Transaction Value
Dust Attack
Previously, AMBCrypto had reported a strange network activity behind Litecoin’s active addresses; a pattern was witnessed on 20 August 2019 after James Jager, Project Lead at Binance Academy, first identified the attack.
Addressing the same, Litecoin.com’s Franklyn Richards had noted that the active address figure spiked to over 70,000 before abruptly dropping back down, resulting in a sawtooth-like pattern.
This behavior continued until January and the latter part of February this year, with brief breakouts, thrice.
Notably, the total number of transactions did not record any surge during the same time period nor did the average value being sent exhibit any signs of a correlation.
A dust attack is essentially when a scammer sends the smallest denomination of crypto [1 Litoshi] to the target wallet. Since the amount sent is pretty much negligible, the victim often never notices it. Hence, the term dust. This is done so that every time the target user makes their next transaction [even with the anonymous tools], the small amount can be tracked by the malicious entities.
After the attack, the Litecoin Foundation had advised its users to use different addresses for transacting funds. Using VPNs to confuse blockchain surveillance tools was also recommended by the Foundation. Further, a victim, who is already under a dust attack may convert all their affected coins into another cryptocurrency to avoid being tracked.






